CISOs & Cyber Defence Professionals
Stop Guessing If Your Defences Work. Continuously validate your security controls against the latest threats.
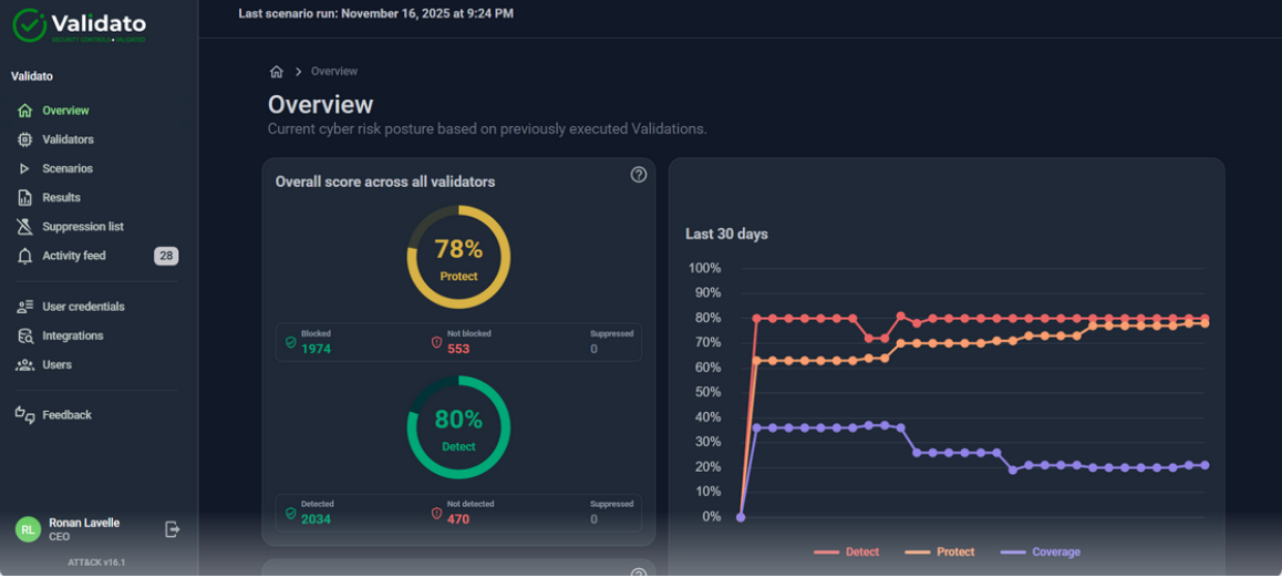
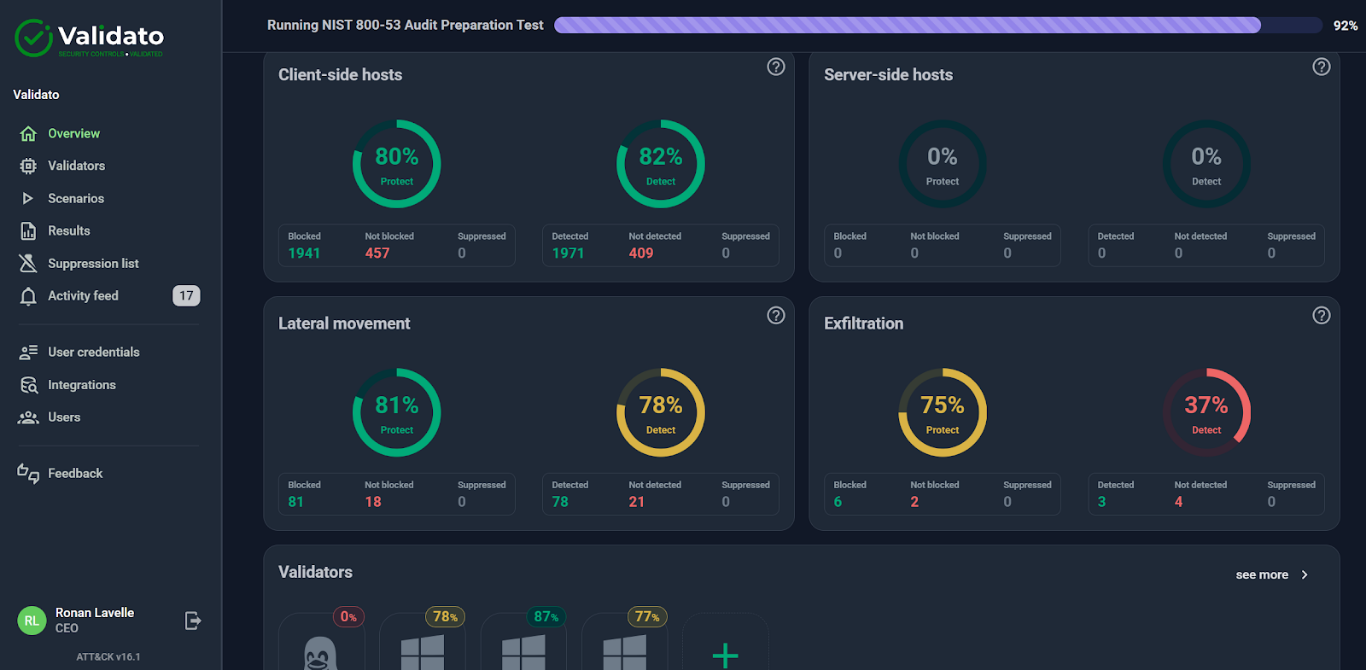
Validato – Continuous Security Control Validation
Know exactly where your defences fail — and fix them — before attackers find out.
- Simulate real-world threats
- MITRE ATT&CK framework
- Unbised, quantifiable data
- DORA & NIS2 operational resilisence
Trusted By:

Operational in 30 Minutes

Windows, Linux & Mac

DORA & NIS2 Compliance Aide
Demonstrate Your Operational Resilience to Cyber Threats
The Visibility Gap
Most organisations can’t prove their security actually works. Static assessments leave hidden gaps that adversaries don’t miss.
The Cost of Assuming You Are Secure
What Our Customers Say About Validato
Validato is a founder member of the MITRE ATT&CK User Group in Europe, called the MITRE ATT&CK Special Interest Group in collaboration with MITRE, KPMG and ISACA.
Join the LinkedIn community here.
Modern Problems Require Modern Validation
Traditional security testing methods are no longer sufficient to meet operational resilience standards
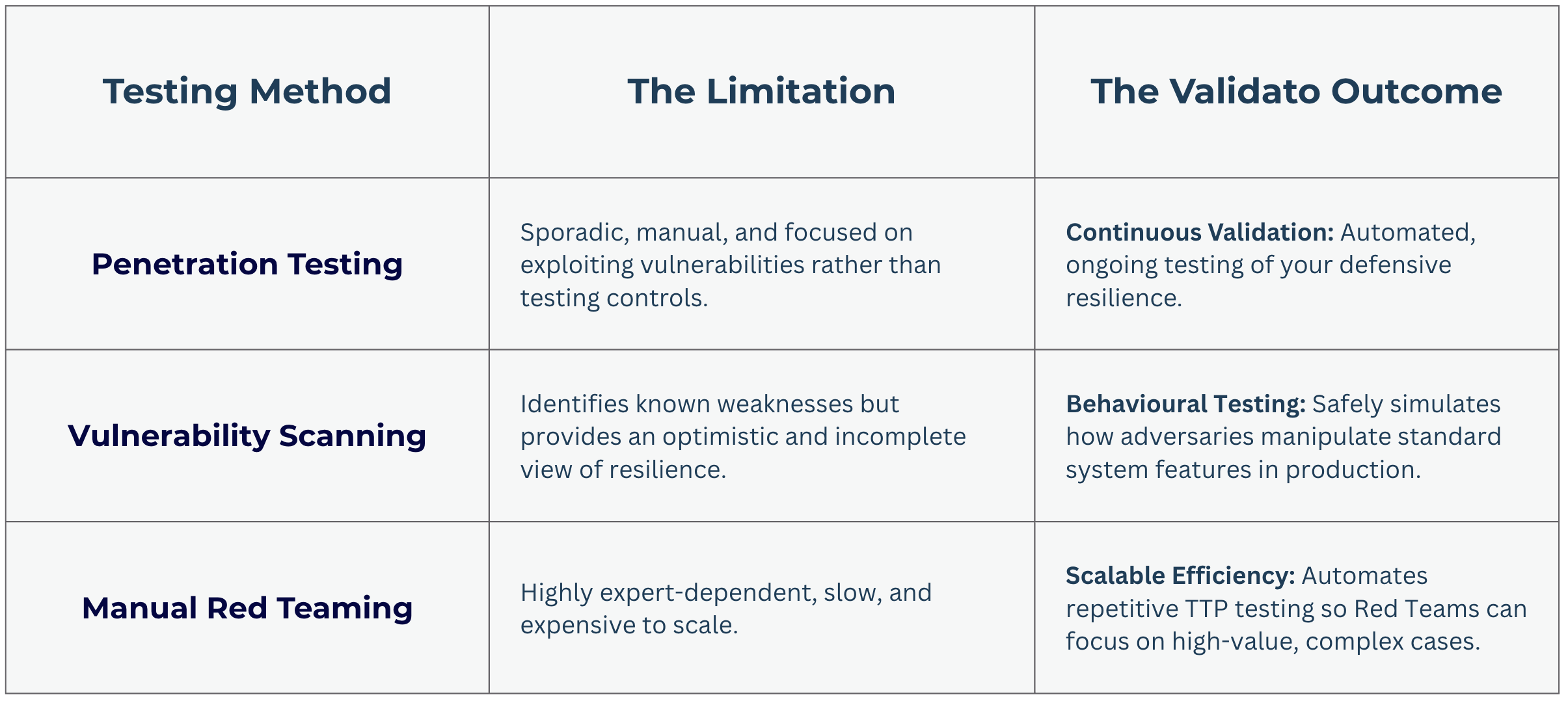
Why Security Leaders Are Switching To Continuous Validation
Validato transforms a compliance burden into an automated, cost-effective strategy for enhancing cyber resilience