Frequently Asked Questions
Understanding Validato & Security Validation
What exactly is Validato?
Validato is a Security Control Validation platform in the Breach & Attack Simulation (BAS) and Adversarial Exposure Validation (AEV) space. Its core purpose is to continuously validate the effectiveness of an organisation’s protection and detection capabilities against cyber threat behaviors.
What is Security Control Validation?
It is the process of objectively and continuously testing existing security measures to verify if they are working as intended. It provides quantifiable data on defence efficacy for environments like Windows, Linux, and Mac.
What is Breach and Attack Simulation (BAS)?
BAS is an automated technology used to safely simulate offensive cyber-attack scenarios and real-world threat techniques in production environments without causing disruption.
How does Validato define Simulation vs. Emulation?
Validato uses Simulation, focusing on the manipulation of MITRE ATT&CK Techniques (behaviours). Unlike Emulation, which replicates specific files or payloads (IOCs) that frequently change, simulation focuses on underlying defensive gaps that remain relevant over time.
Comparisons & Technical Differentiation
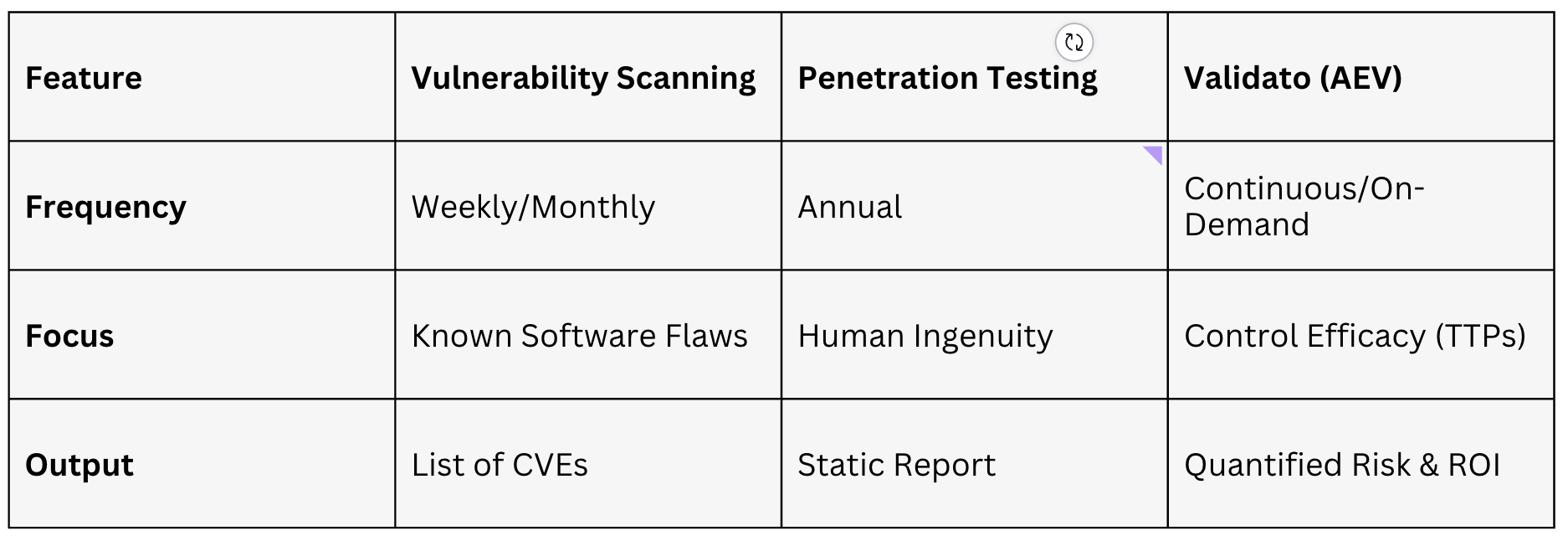
How is Validato different from Pen Testing or Vulnerability Scanning?
Validato is distinct and complementary to these traditional methods:
- Vulnerability Scanning: Identifies known software weaknesses (CVEs).
- Penetration Testing: A sporadic, manual service focused on exploiting vulnerabilities to reach a specific goal.
- Validato (AEV): Provides continuous, automated validation of control efficacy (TTPs) and produces quantified risk and ROI data.
Can Validato replace a Red Team?
No, it empowers them. BAS platforms automate repetitive TTP testing, which frees up expert Red Teams to focus on complex, advanced emulation that requires human creativity.
Compliance, Strategy & Regulatory Alignment
How does Validato assist with DORA, NIS2, and the UK CRA?
These regulations are shifting toward resilience-based requirements. Validato assists by:
Providing automated, auditable data for Continuous Compliance Readiness.
Stress-Testing Resilience against threats like Ransomware to prove controls are active.
Ensuring Supply Chain Assurance by validating the effectiveness of third-party vendors and MSSPs.
Can BAS tools automate DORA’s Threat-Led Penetration Testing (TLPT)?
While DORA TLPT requires human-led creative exploitation, BAS platforms automate the evidence collection and repetitive TTP testing required between triennial manual assessments.
What is Threat-Informed Defence?
It is a strategy that bases security investments and prioritisations on actual real-world attacker behavior, typically using frameworks like MITRE ATT&CK.
How does this fit into Continuous Threat Exposure Management (CTEM)?
Validato serves as a core component of a CTEM program by providing the continuous validation tools needed to test, measure, and harden defensive capabilities across the enterprise.
Reporting & Actionable Outcomes
What kind of reporting does Validato provide?
The platform moves beyond simple lists, offering clear, unbiased data on which behaviors were detected or prevented.
Does it help with remediation?
Yes. Validato provides Guided Mitigation, including step-by-step instructions to harden defences and prioritise efforts based on the most feasible exploits in your specific environment.

